The digital world we’re currently living in is constantly evolving; there’s no denying it. As new technologies and applications come with new vulnerabilities and threats, regulatory compliance and data protection stand as two crucial principles guiding these advancements and industries forward, including software-as-a-service (SaaS) applications.
As SaaS providers navigate through the complicated maze of compliance regulations, such as the General Data Protection Regulation (GDPR), the California Consumer Privacy Act (CCPA), the Payment Card Industry Data Security Standard (PCI DSS), and the Health Insurance Portability and Accountability Act (HIPAA), ensuring complete compliance with these standards becomes of vital importance.
At the heart of regulatory compliance and data protection lie a slew of essential security measures, ranging from data encryption and access controls to regular security audits, incident response planning, and, most importantly, data decommissioning processes. Whether it’s physical security, cybersecurity, or other methods and measures, it is crucial that the two always go hand-in-hand.
Essential Security Measures and Methods
Data Encryption
Data encryption stands as an essential tool, not just for SaaS providers but for any organization or company handling sensitive information. By converting the information into an encrypted format, SaaS providers (and their customers) can rest assured knowing that even in the off chance the data is compromised, it will remain indecipherable to unauthorized accessors. This encryption process requires complex algorithms to essentially scramble the data into ciphertext, which can only be decrypted with the corresponding decryption key, which is typically held by authorized users (think like a treasure chest that can only be opened by a one-of-a-kind, magical key).
Implementing robust encryption protocols not only helps SaaS providers comply with regulatory mandates but also instills confidence and trust among customers regarding the security of their data. With data encryption in place, SaaS providers can begin to mitigate the risk of potential thefts, maintain confidentiality, and uphold the integrity of their systems and services.
Access Controls
The next crucial cybersecurity reinforcement are access controls that restrict data access to only those with permission and clearance.
Access controls serve as a critical layer of defense for SaaS providers, ensuring that only authorized individuals can access sensitive data and resources. Key cards, PINs, biometric authentication, multi-factor authentication, and other secure methods all play a role in verifying the identity of those seeking entry. By restricting access to data and functionalities to only those with specific roles or privileges, access controls help prevent unauthorized access, data breaches, and insider threats.
Additionally, access controls play a heavy role when adhering to compliance regulations and mandates, ensuring that data is accessed and handled while aligning with their corresponding privacy and security standards.
Regular Security Audits
Regular security audits are just one phenomenal proactive risk management tool for identifying vulnerabilities while adhering to compliance standards. Scheduled assessments of systems, processes, and controls give SaaS providers the power to identify any potential or existing vulnerabilities, assess the effectiveness of their already existing security measures, and mitigate them. These audits not only help to detect and address security weaknesses but also showcase a transparent commitment to maintaining robust security practices, something partners, customers, and investors are looking for when it comes to their sensitive information.
Incident Response Planning
Another effective proactive tool for optimal SaaS cybersecurity is implementing a stringent incident response plan. An incident response plan is an indispensable tool for not just SaaS providers but everyone, as it outlines clear protocols for incident detection, proper communication channels for reporting and escalation, and predefined roles and responsibilities for all of their key stakeholders.
Incident response planning can also include regular drills and simulations to test the plan’s efficiency and effectiveness while also ensuring that all personnel are ready to handle whatever security incident is thrown their way. (We do fire drills for a reason, so why not do them when it comes to our own data?) By prioritizing incident response planning, SaaS providers can minimize the potential damage of security breaches, preserve data integrity, and uphold customer trust in their ability to safeguard sensitive information.
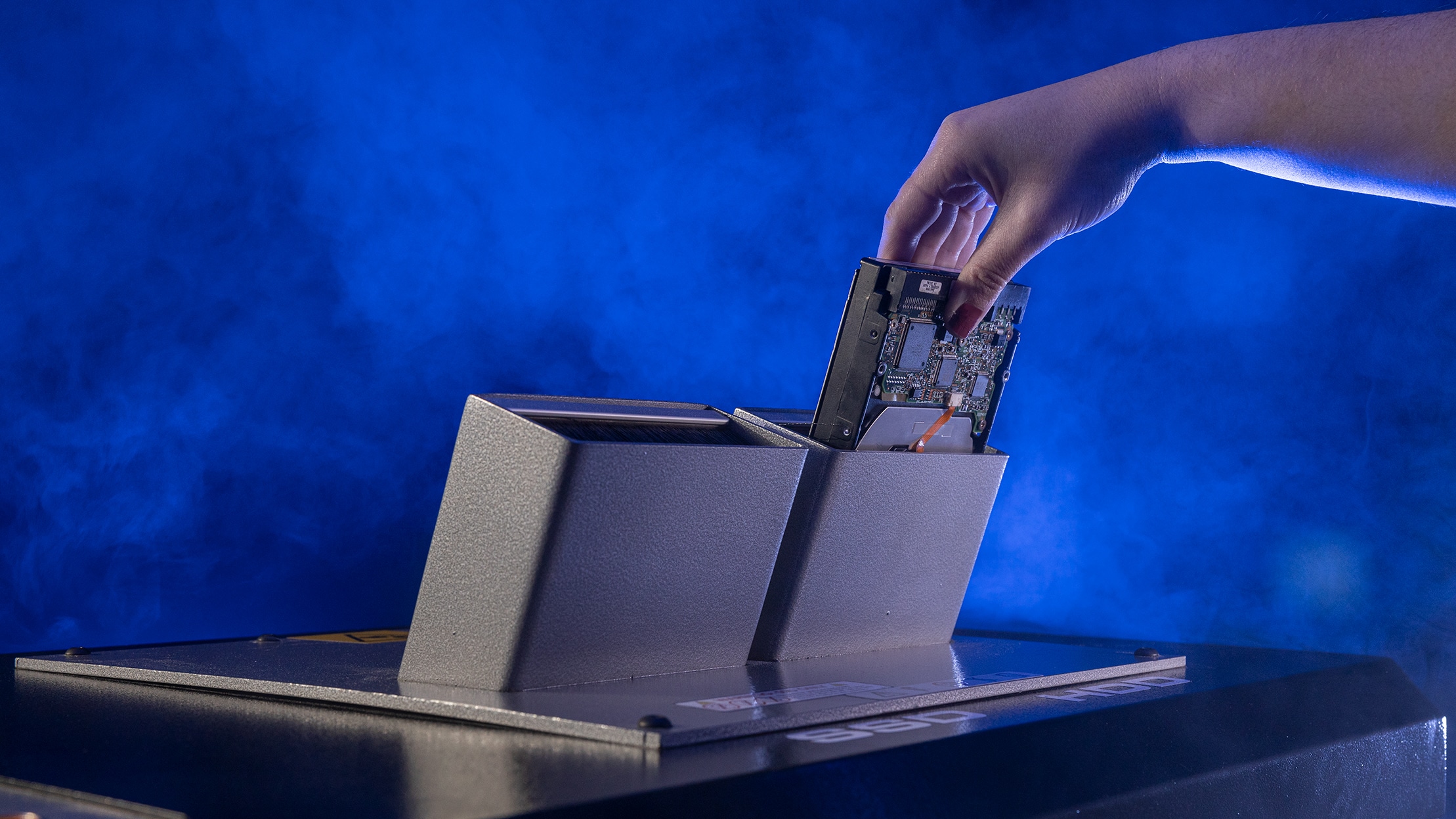
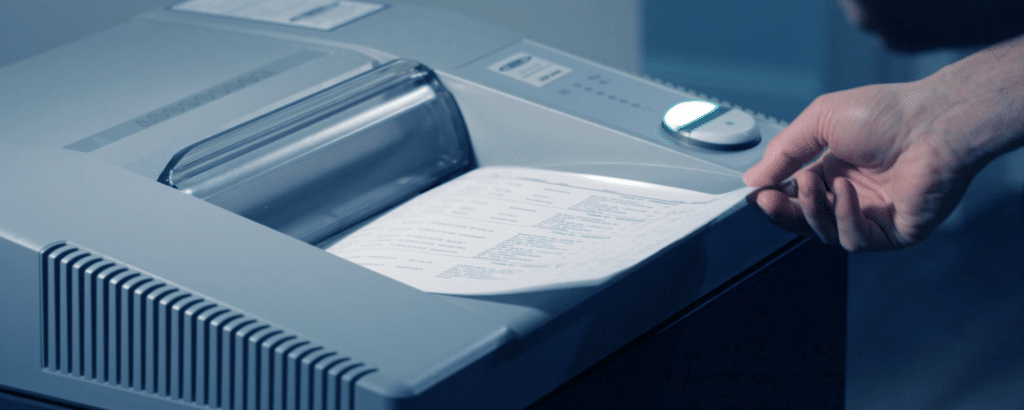
In-House Data Decommissioning Processes
The last and most crucial step of any data lifecycle management strategy is a high-security data decommissioning process, preferably in-house. We all know this. Otherwise known as data destruction, proper data decommissioning is the process of securely and responsibly disposing of any data considered “end-of-life.” Data decommissioning should be applied to any device that can store data, such as hard disk drives (HDDs), paper, optical media, eMedia, solid-state drives (SSDs), and more.
When data is properly managed and disposed of, organizations can better enforce data retention policies. This, in turn, leads to improved data governance and gravely reduces the risk of unauthorized or illegal access. As critical as data decommissioning is, having it done in-house provides an added layer of security when ensuring that all sensitive data is disposed of properly. Additionally, it assists companies in adhering to data protection laws like GDPR and HIPAA, which frequently call for strict, safe data disposal procedures.
Compliance Regulations
As SaaS providers handle vast amounts of sensitive data, ensuring compliance with regulations is crucial, but compliance regulations are not a one-size-fits-all fit. Each regulation brings its own set of requirements, implications, and parameters, along with its own list of consequences and fines.
To keep it brief, here is just a small list of compliance regulations SaaS providers should be in accordance with.
Financial Compliance
- ASC 606: ASC 606 is a security framework that was developed by the Financial Accounting Standards Board (FASB) and the International Accounting Standards Board (IASB). It’s a five-step process that allows businesses and organizations to accurately and transparently reflect the timing and amount of revenue that is earned.
- Generally Accepted Accounting Principles (GAAP): GAAP, also developed by FASB, is a collection of accounting rules and best practices that U.S. law mandates when it comes to releasing public financial statements, such as those traded on the stock exchange.
- International Financial Reporting Standards (IFRS): IFRS is a set of global accounting guidelines that apply to a public corporation’s financial statements in order to show transparency, consistency, and international comparison.
Security Compliance
- International Organization for Standardization (ISO/IEC 27001): ISO/IEC 27001 is an internationally recognized standard for information security management systems and provides a framework for identifying, analyzing, and mitigating security risks.
- Service Organization Control (SOC 2): SOC 2 was developed by the American Institute of CPAs (AICPA) to be a compliance standard that defines the criteria for managing customer information within service organizations.
- Payment Card Industry and Data Security Standard (PCI DSS): PCI DSS is a set of security protocols that must be adhered to by any company that handles payment processes, such as accepting, transferring, or storing card financial data.
Data Security and Compliance
- General Data Protection Regulation (GDPR): GDPR is a personal data protection law that requires stringent data protection standards for businesses and organizations that handle personal data of EU citizens, regardless of where the business operates from. With GDPR, EU residents are able to view, erase, and export their data, and even object to the processing of their information.
- Health Insurance Portability and Accountability Act (HIPAA): HIPAA is an American federal law that protects sensitive patient health information (PHI) from being shared without their consent.
- California Consumer Privacy Act (CCPA): CCPA is essentially like GDPR but for California residents, granting them greater control over their personal information and necessitating transparent data collection practices and opt-out mechanisms.
Conclusion
In conclusion, for SaaS providers, regulatory compliance and data protection represent not just legal obligations but also opportunities to foster customer trust and optimize their data security measures. By implementing essential security measures, adhering to regulatory frameworks, and embracing a culture of continuous improvement, SaaS providers can navigate the regulatory landscape with confidence, safeguarding both data and reputation in an increasingly digitized world.
At SEM, we have a wide array of high-security data destruction solutions that are specifically designed to meet any volume and compliance regulations, whether in the financial, healthcare, payment card, or other industries. In a time when the digital space has the power to influence the course of multiple industries, implementing essential security methods along with a decommissioning plan are crucial tools that determine an industry’s robustness, legitimacy, and identity.