Ah, tax season. A time to reflect and reevaluate on the past year’s finances, and a wonderful excuse for some major spring cleaning!
In this blog, we’ll break down all of the documents you can say, “bye-bye” to and the ones you may want to keep around for a bit longer. It’s important to note that this is simply a condensed breakdown, but more information on record retention policies (RRP) can be found in our blog, Records Retention Schedules: When Will Your Data Expire?
Bye-Bye Junk!
- ATM and deposit receipts: These can be shredded once they are compared against your monthly statement.
- Credit card bills: Once your bill has been paid, shred away!
- Utility bills: Keeping utility bills once they are paid is not always necessary. However, it is recommended to save all of your utility bills for one year if you are claiming a home office deduction.
- Pay stubs: Pay stubs should be saved for one year but once your taxes are filed, they are ready for the shredder.
- Insurance policies: Once your policy is renewed (either with the same insurance company or a different one), feel free to feed it to your shredder.
- Receipts: No need to pile up your desk or filing cabinet with every UberEats and Postmates receipt from the past year. It is only necessary to keep receipts from bigger purchases or items that will be deducted.
- Monthly bank statements: Your monthly bank statements should be saved for one full year and then shredded after you receive your annual statement.
- Monthly investment statements: All annual statements and the most recent monthly statement should be kept on file; however, feel free to shred the rest!
Documents for Next Tax Season
- Income: Whether your income comes from wages, interest, or other business, any W-2, 1099, or K-1 forms, and bank and brokerage statements should be kept leading up to your next tax return.
- Deductions and credits: Any receipts pertaining to childcare, medical and dental expenses, using your home as your business, alimony, or charitable donations should be kept leading up to your next tax return. In addition, any receipts or invoices, cancelled checks, and bank or credit card statements.
- Home and property documents: Whether they are closing statements, proof of payments, insurance records, or home and property renovation receipts, these types of documents should all be kept for a year leading up to tax season.
- Investments: Any and all 1099 and 2439 forms, brokerage statements, and mutual fund statements should also be kept prior to filing your taxes.
With all of this being said, it is important to mention that there are some financial documents that should be kept for a specific amount of time after you file your taxes. The Internal Revenue Service (IRS) has three years to assess additional tax and audit returns, meaning it would be a smart move to keep any documentation to support your recent claim should be kept on file.
Shred Away!
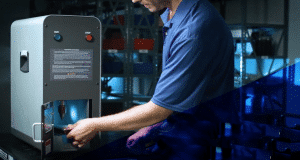
Now is the fun part: shredding time! While there are various ways to destroy a paper document (as detailed in our recent blog, How NOT to Destroy Paper Documents), we at SEM know it to be best practice to use a high security paper shredder (no, big box store shredders won’t cut it — pun intended!) when destroying all of your end-of-life paper documents. By adopting a secure shredder policy, you can be sure your financial information does not get into the wrong hands. We suggest the SEM Model 1324P deskside shredder for all of your at-home shredding needs. This device offers a DIN 66399 P-4 particle.

At SEM we have an array of high-quality NSA listed/CUI and unclassified paper shredders to meet any regulation. Any one of our exceptional sales team members are more than happy to help answer any questions you may have and help determine which machine will best meet your destruction needs.